-
Categories
- Video Games Accessories
- Stands
- Audio Controller
- Cameras
- Chargers & Connecters
- Console Accessory Set
- Console Charger
- Console Charging Cable
- Console Cooling System
- Console Cover
- Console Display Protection
- Console Faceplate
- Console Hand Strap
- Console Hard Disc Drive
- Console Holder
- Console Link Cable
- Console Loudspeaker
- Console Power Supply
- Console Replacement Stick
- Console Starter Set
- Console Sticker
- Controllers & Joysticks
- Cycle Pedal
- Display Stand
- Electronic Dancing Mat
- Fight Arena
- Game Case
- Gamepad
- Gaming Glove
- Gaming Keyboard & Mice
- Gaming Pedals
- Gaming Seats
- Guitar
- Joystick
- Microphone & Headsets
- Pistol/Gun
- Replacement Accessories
- Skateboard
- Ski
- Snowboard
- Steering Wheel
- Virtual Reality
- Controller Cover
- Home Audio Equipment
- Amplifiers/Pre-Amplifiers
- Audio Cassette Decks
- Audio Jukeboxes
- Audio MD Decks
- Audio Receivers/Tuners/Radios
- CD Decks
- Effects Equipment
- Home Stereo - Systems
- Home Theatre - Systems
- Karaoke Systems
- Speaker Systems
- Turn Table - CD
- Turn Table - Vinyl
- Visual Mixers
- Subwoofers
- Floor Standing Speakers
- Soundbars
- Karaoke Microphones
- Home Appliances Accessories
- Soap Dispenser
- Iron Board
- Bearing
- Beverage Flavouring
- Bottle
- Burner Cover
- Carbonator
- Coil
- Control Knob
- Conversion Top
- Cooker Hood Ducting
- Cooker Hood Reducing Socket
- Dishwasher Tray
- Drain Hose Set
- Drawer
- Drip Bowl
- Drum Belt
- Drum Seal
- Drying Rack
- Extractor Fan Filter
- Filter
- Floor Polisher Brush
- Gas Burner Bib
- Grill Pan/Tray
- Heat Diffuser
- Hinge Parts
- Hob Guard
- Hose Clip
- Hose Connector
- Ice Cube Tray
- Ice Maker Kit
- Inlet Hose
- Knob/Button
- Laundry Pedestal
- Laundry Stacking Kit
- Lint Screen
- Microwave Turntable Platter
- Module
- Nozzle
- Oven Element
- Oven Rack
- Power Cord
- Range Cord
- Refrigerator Deodorant Filter
- Refrigerator/Freezer Digital Thermometer
- Replacement Door
- Replacement Handle
- Replacement Lid/Cap
- Shelf
- Splash Back
- Spray Bar
- Stove Knob Cover
- Tumble Dryer Condenser
- Tumble Dryer Vent Hose
- Vacuum Cleaner Clip
- Vacuum Cleaner Crevice Tool
- Juicer
- Masticating Juicer
- Microhood Microwave Ovens
- Microwave
- Mincer
- Mixer
- Mixer Grinder
- Oven
- Over-the-range Microwave Ovens
- Personal Size Blender
- Portable Thermo Cool Box
- Rotisseries and Roasters
- Sewing Machine
- Sharpener
- Shoe Cleaner/Polisher
- Skillet
- Speed-cooking Microwave Ovens
- Stand Mixer
- Toaster
- Water Dispenser
- Water Purifier
- Wet Grinder
- Wok
- Handheld Vacuums
- Robotic Vacuum
- Small Appliances
- Scales
- Sweeper
- Boiler
- Can Opener
- Centrifugal Juicer
- Chopper
- Citrus Juicer
- Compact Microwave Ovens
- Compact Refrigerators
- Convection Oven
- Countertop blender
- Countertop Burners
- Countertop Microwave Ovens
- Countertop Oven
- Dehydrator
- Disinfecting Cabinet
- Dough Blender
- Electric Griddle
- Food Grinder
- Food Processor
- Frozen Drinks Maker
- Garbage Disposal
- Grater
- Hand blender
- Hand Mixer
- Ice Shaver
- Insect Killer
- Iron
- Specialty Electrics
- Air Fryer
- Beverage Dispenser
- Bread Maker
- Burner
- Butter Maker
- Candyfloss Machine
- Carbonated Drinks Maker
- Chapatti Maker
- Chocolate Fountain
- Contact Grill
- Cookie Guns
- Cooking Timer
- Crepe Maker
- Cupcake & Cookie Maker
- Deep Fryer
- Doughnut Maker
- Drink Fountain
- Egg Cooker
- Electric Can Openers
- Electric Shoe Cleaner/Polisher
- Electric Slicers
- Electric Wine Bottle Opener
- Fondues
- Hot Dog Roller
- Hot Plate
- Hot Stone
- Ice Cream Maker
- Ice Maker
- Indoor Grills & Panini Presses
- Induction Burner
- Knife Sharpener
- Mills
- Paella Maker
- Pancake Maker
- Pasta Machine
- Pizza Maker
- Pizzelle Maker
- Popcorn Maker
- Quesadilla and Tortilla Maker
- Raclettes
- Revolving Spit Rotisserie
- Rice Cooker
- Samosa Maker
- Sandwich Maker
- Slow Cookers
- Soda Maker
- Sous Vide
- Sparkling Water Machine
- Tangines
- Vacuum Sealer
- Large Appliances
- Dryer
- Air Conditioner
- Air Cooler
- Air Ionizer
- Air Purifier
- Chiller
- Chimney Hood
- Cooking Range
- Cooktop
- Dehumidifier
- Dish Washer
- Humidifier
- Kitchen Hob
- Refrigerator
- Room Heater
- Stove
- Warming Drawer
- Washing Machine
- Wine & Beer Fridge
- Canister Vacuum
- Stick Vacuum
- Upright Vacuum
- Wet & Dry Vacuum
- Ceiling Fans
- Pedestal Fans
- Table Fans
- Exhaust Fans
- Tower Fans
- Cutlery & Flatware
- Bread Knife
- Carving & Slicing Knife
- Cheese Knife
- Chef Knife
- Chopsticks
- Cleavers & Boning Knife
- Cutlery Set
- Cutlery Tray
- Cutting Boards
- Flatware Caddy
- Flatware Set
- Fork Set
- Forks
- Fruit & Vegetable Knife
- Kitchen Shears
- Knife Accessories
- Knife Block & Storage
- Knife Set
- Knifes
- Other Knifes
- Paring Knife
- Place Setting
- Serving Pieces
- Serving Set
- Sharpener & Steel
- Specialty
- Bar
- Chiller
- Carbonator
- Ice Cube Tray
- Coasters
- Bottle Opener
- Cocktail Pick
- Cocktail Shaker
- Cork Screw
- Decanter
- Foil Cutter
- Garnishing Tool
- Ice Crusher
- Ice Molds
- Ice Stray
- Ice Tools & Buckets
- Jigger
- Other Bar Tools
- Set
- Specialty Tool
- Strainers & Stirrers
- Tongs
- Wine Accessories
- Wine Aerator
- Wine Glasses
- Wine Opener
- Storage & Organization
- Lunch Bag
- Bag
- Other Storage
- Aluminium Foil
- Biscuit & Cookie Jar
- Bread Box
- Cabinet & Drawer Organization
- Carton
- Clamshells (Hinged)
- Cling Film
- Compost
- Cooler
- Countertop & Wall Organization
- Dinnerware & Stemware Storage
- Flatware & Utensil Storage
- Food Containers
- Food Saver
- Food Wrap Dispenser
- Pods
- Racks
- Sink Sets
- Spice Jars
- Storage Bottles
- Coffee & Tea Appliances
- Beverage Warmers
- Capsule System Coffee Maker
- Coffee Grinder
- Coffee Maker
- Drip Coffee Maker
- Electric Coffee Percolators
- Electric Kettle
- Espresso Maker
- French Press & Pour-Over
- Golden Cup Coffee Maker
- Iced Tea Machines
- Milk Frother
- Mocha Maker
- Percolator
- Pod System Coffee Maker
- Portafilter System Coffee Maker
- Cycling
- Cycling Accessories
- Sunglasses
- Protective Gear
- Bike Tools & Equipment
- Comfort & Cruiser Bikes
- Freestyle Bmx Bikes
- Hybrid Bikes
- Lights & Reflectors
- Mountain Bikes
- Road Bikes
- E-Bikes
- Fat Bikes
- Cycling Helmet
- Cycling Tyre Tubes
- Cycling Pumps And Gas Tanks
- Cycling Car Racks Carriers
- Bike Cases And Travel Bags
- Bike Saddle Bags And Tube Bags
- Bike Stands And Storage
- Cycling Bells
- Reflective Vests And Stickers
- Bike Fenders
- Baby Carriers And Trailers
- Bike Locks
- Cycling Phone Mounts
- Bottle Cages
- Hydration Systems
- Cycling Baskets
- Bike Trainers And Rollers
- Cycling Power Meters
- Cycling Computers And Sensors
- Cycling Road Groupsets
- Cycling Derrailleurs
- Cycling Cassettes
- Cycling Chains
- Cycling Brakes
- Cycling Pedals
- Cycling Cranksets
- Cycling Saddles
- Cycling Handlebars
- Cycling Wheels
- Cycling Rims
- Cycling Jackets
- Cycling Chamois
- Cycling Triathlon Suits
- Cycling Vests
- Cycling Hats
- Cycling Gloves
- Cycling Socks
- Cycling Shoes
- Cycling Endurance Wet Suits
- Strength Training Equipment
- Adjustable Fitness Benches
- Arm Machines
- Back Machines
- Benches
- Core & Abdominal Trainers
- Dip Stands
- Dumbbells
- Hand Strengtheners
- Home Gyms
- Inversion Equipment
- Kettlebells
- Leg Machines
- Medicine Balls
- Power Cages
- Pull-Up Bars
- Pushup Stands
- Smith Machines
- Suspension Trainer
- Weight Bands
- Weight Lifting
- Weight Lifting Belts
- Weight Vests
- Weights
- Ankle Weight
- Wrist Weight
- Clubbell
- Weight Lifting Bar
- Weight Lifting Plate
- Dumbbell Rack
- Free-Weight Rack
- Plate Storage Rack
- Plate Rack
- Strength Training Rig
- Resistance Trainer
- Lifting Grips
- Training Ladder
- Shoulder Machine
- Abs Machine
- Training Marker Cone
- Boxing & MMA
- Gloves
- Protective Gear
- Sets
- Boxing Foot Gear
- Boxing Gym Equipment
- Boxing Training Gloves
- Equipment Bags
- Hand Targets & Focus Mitts
- Hand Wraps
- Ninja Weapons
- Punch Bag Accessories
- Punch Bags
- Shoes
- Training Equipment
- Weapon Cases
- Weapon Stands
- Weapons
- Speedbags
- Boxing Gloves
- Mma Gloves
- Muay Thai Gloves
- Karate Gloves
- Karate Kimono
- Judo Kimono
- Jiu Jitsu Kimono
- Boxing Shorts
- Grappling Rashguards Spats
- Mma Belts
- Shin Guards
- Martial Arts Headgear
- Chest Pads
- Thigh Pads
- Elbow Pads
- Belly & Body Pads
- Kick Shields
- Forearm Pads
- Cups/Groin Guards
- Buoyancy Compensators
- Buoyancy Vests
- Communication Devices
- Diving Fin Bags
- Diving Fins
- Diving Gloves
- Diving Hoods
- Diving Lights
- Diving Masks
- Diving Socks
- Diving Suits
- Diving Tanks
- Diving Valves
- Diving Weights & Belts
- Dry Boxes
- Duffles
- Gauges
- Mask Defoggers
- Octopuses
- Reels
- Regulator Accessories
- Regulators
- Roller Bags
- Diving & Snorkelling
- Backpacks
- Air Decompression Limit Monitors
- Sports & Outdoor Play
- Sports
- Balls
- Beanbags & Foot Bags
- Blasters & Foam Play
- Bubbles
- Fitness Equipment
- Gym Sets & Swings
- Inflatable Bouncers
- Kickball & Playground Balls
- Kites & Wind Spinners
- Lawn Games
- Play Sets & Playground Equipment
- Play Tents & Tunnels
- Playhouses
- Trampolines
- Yo-yos
- Pools
- Pool Covers & Accessories
- Pool Floats
- Rafts
- Boats
- Water Blasters & Soakers
- Water Slides
- Swim Gear
- Hobbies
- Coin Collecting
- Hobby Building Tools & Hardware
- Hobby RC Vehicles & Parts
- Model Building Kits & Tools
- Models & Model Kits
- Radio Control
- RC Vehicles & Parts
- Scaled Model Vehicles
- Slot Cars Race Tracks & Accessories
- Stamp Collecting
- Trains & Accessories
- RC Vehicles & Batteries
- RC Airplanes
- RC Cars & Trucks
- RC Helicopters
- RC Quadcopters
- Baby Furnishing
- Baby Bedding
- Baby Bedding Accessories
- Baby Blankets
- Baby Bouncing Cradles
- Baby Chairs/Armchair/Bean Bags
- Baby Cots
- Baby Cots/Cot Beds/Cradles
- Baby Cradles
- Baby Cupboard
- Baby High Chair
- Baby Laundry Hampers
- Baby Organisers
- Baby Play Pens/Dens
- Baby Potties/Training Seats
- Baby Rocker
- Baby Storage Box
- Baby Swaddle
- Baby Swings
- Baby Walkers
- Baby Wraps
- Changing Tables
- Cradles
- Nursery Decor
- Nursing Pillow
- Mirrors
- Pillows
- Bassinet Bedding
- Blankets & Swaddling
- Cradle Bedding
- Crib Bedding
- Gift Sets
- Pillow Protectors
- Pillowcases
- Playard Bedding
- Quilts & Bed Covers
- Toddler Bedding
- Parts & Accessories
- Tables & Chairs
- Changing & Dressing
- Furniture Collections
- Gliders, Ottomans & Rocking
- Other Nursey Furniture
- Mobiles
- Rugs
- Wall Decor
- Window Treatments
- Baskets & Liners
- Bookends
- Christening
- Clocks
- Door Hangers
- Drawer Handles
- Hand & Footprint Makers
- Keepsake Boxes & Tins
- Keepsake Frames
- Keepsake Rattles
- Lamps & Shades
- Memory Boards
- Night Lights
- Picture Frames
- Silver Baby Spoons
- Sleep Soothers
- Feeding & Training Accessories
- Combination
- Baby Sippy Cup
- Baby Blocks Freezer Storage Containers
- Baby Cutlery
- Baby Food Maker
- Baby Formula/Snack Dispenser
- Bibs
- Bottle Accessories
- Bottle Teats
- Bottle Warmers
- Bowl Grip Mats
- Breast Milk Bag
- Breast Pumps Electric/Manual
- Feeding Bottles
- Feeding Bowls
- Feeding Placemat
- Feeding Plates
- Food Dispensing Spoon
- Food Pouch
- Food Pouch Adapter
- Food Storage Containers
- Gum Massagers
- Lunch Bag
- Baby Lunch Box
- Lunch Set
- Nipple Shields/Accessories
- Plate With Spill Catcher
- Prep Filters
- Shears
- Snack/Lunch Bag
- Steriliser
- Tableware
- Weaning and Drinking Kit
- Teethers
- Baby Bottle Drying Rack
- Milk Powder Dispensers
- Formula Preparation Machine
- Baby Booster Seat
- Pacifiers
- Pacifier Accessories
- Teething Gels
- Baby Bottle Cleaning Sponges
- Baby Bottle Cleaning Liquid
- Highchair Tray
- Highchair Cushion
- Burpcloths
- Baby Safety Equipment
- Baby Bath Gate
- Baby Door Bouncers
- Baby Door Stopper
- Baby Harnesses/Reins
- Baby Safety Bed Rail
- Baby Safety Corner Protector
- Baby Safety Cot Bumper/Pad
- Baby Safety Lock
- Baby Safety Net
- Baby Safety Night Light
- Baby Safety Socket Protector
- Baby Safety Stair Gate
- Bath Spout Cover
- Bath Thermometer
- Bathing Protect Soft Cap Hat
- Bathing Safety Mat
- Finger Pinch Guard
- Large Tub Guard
- Lid Lock
- Room Thermometer
- Sign Board
- Fresh Vegetables
- Baby Spinach
- Banana Leaves
- Beans
- Chili Peppers
- Corn
- Garlic
- Green Peas
- Broccolini
- Mushroom
- Sea Vegetables
- Shiitake Mushrooms
- Tomato
- Truffles
- Capsicum
- Asparagus
- Chilly
- Coriander
- Basil
- Bay Leaves
- Snow Peas
- Curry Leaves
- Broccoli
- Cabbage
- Cauliflower
- Chicory
- Chives
- Cilantro
- Fresh Coleslaw
- Cucumber
- Fresh Parsley Chopped
- Dill
- Eggplant
- Fennel
- Galanga
- Leafy Greens
- Lemon Grass
- Marjoram
- Kailan
- Mint Leaves
- Mushrooms & Truffles
- Onion
- Oregano
- Parsley
- Kale
- Kohlrabi
- Peppers
- Leeks
- Potato
- Lemon Leaves
- Root Vegetables
- Rosemary
- Sage
- Squash & Gourds
- Tarragon
- Thyme
- Snake Guard
- Lettuce
- Looki
- Beetroot
- Carrot
- Celery
- Ginger
- Lotus Root
- Okra
- Radish
- Drumstick
- Bitter Gourd
- Yam
- Tindly
- Tapioca
- Turnips
- Spinach
- Chayote
- Marrow
- Mixed Vegetables
- Noodles Veg Mix
- Onion Spring
- Panden Leaves
- Parsnips
- Rhubarb
- Rocca Leaves
- Indian & Exotic Herbs
- Baby Paksoi
- Cut & Peeled Veggies
- Sprouts
- Fresh Fruits
- Cut Fruit
- Applesauce & Fruit Cups
- Apricots
- Artichokes
- Pineapple
- Apples
- Avocados
- Bananas
- Berries
- Citrus Fruits
- Dates
- Grapes
- Melons
- Peaches
- Pears
- Plums
- Raisins
- Tropical & Exotic Fruit
- Papayas
- Mangos
- Pumpkins
- Pomegranates
- Persimmons
- Guavas
- Kiwis
- Nectarines
- Sweet Tamarind
- Chickoo
- Coconuts
- Apple Green Sanitised
- Apple Red Sanitised
- Berries Red Current
- Blueberries
- Coconut Water
- Dragon Fruit
- Figs
- Gooseberry
- Granadilla
- Grapefruit
- Kumquat
- Lemon
- Lime Seedless
- Lime Yellow
- Longan
- Mandarin
- Mangosteen
- Orange
- Physalis
- Pithaya
- Salad Dressings
- Salt & Pepper
- Seafood
- Soups Stews
- Spices & Seasonings
- Spreads
- Sugars & Substitutes
- Syrups & Sauces
- Tuna & Fish
- Choco & Nut Spread
- Mayonnaise
- Chilli Sauce
- Soya Sauce
- Dips
- Breakfast & Snack Mixes
- Soups
- Ready To Fry
- Heat & Eat Ready Meals
- Canned, Dry & Packaged Foods
- Baking Decorations
- Baking Mixes & Yeasts
- Canned Fruits
- Canned Vegetables
- Chicken
- Cold Cuts
- Condensed & Powdered Milk
- Flours & Meals
- Honey
- Marmelade & Jams Spreads
- Meat
- Olives
- Packaged Meals & Side Dishes
- Peanut Butter
- Pickles
- Pudding & Gelatin Mixes
- Beverages
- Energy & Sports Drinks
- Juices & Smoothies
- Soft Drinks
- Packaged Water
- Spring Water
- sparkling water
- Soda
- Ground Coffee
- Instant Coffee
- Leaf & Dust tea
- Green Tea
- Tea Bags
- Exotic & Flavored tea
- syrups & concentrates
- Unsweetened & Cold Press
- Cocktail Mix
- Non-Alcoholic Drinks
- Health Drinks & Mixes
- Iced Tea
- Body Parts
- Aerials
- Mirrors
- Accelerator Cable
- Anti-Theft Systems
- Badges & Emblems
- Bonnet & Tailgate Struts
- Bonnet Buffers
- Bonnet Cables
- Bonnet Catch/Locks
- Bonnet Sound Pads
- Bonnet Vents
- Bonnets
- Bumpers
- Cables & Hinges
- Catalytic Converters
- Central Locking Pump & Motor
- Damping Plates
- Door & Roof Seals
- Fuel Tanks & Caps
- Gaskets & Clamps
- Gauges/Clocks/Knobs
- Gear Cables
- Gear Levers & Gaiters
- Glass & Deflectors
- Grilles
- Handles Locks & Barrels
- Heat Exchangers
- Lambda Sensors
- Locking Wheel Kits
- Locks
- Moldings
- Panels
- Pedals & Pedal Rubbers
- Performance Catalysts
- Roof Bar Locking Kits
- Roof Bars
- Seat Adjustment Cables
- Speedo Cables
- Tyres
- Wheel Archs
- Wheel Bolts
- Wheel Caps
- Wheel Nuts
- Wheel Rims
- Window Regulators & Winders
- Engine Parts
- Air Boxes
- Air Filters
- Air Hoses
- Boost Pressure Sensors
- Cam & Valve Train
- Cam Covers
- Car Filters
- Carburettors
- Chain And Tensioner Parts
- Cold Start Valves
- Complete Engines
- Core Plugs
- Cylinder Heads
- Distributor Caps
- Dump Valves
- Electronic Control Units
- Engine Bearings
- Engine Management Sensors
- Engine Management Switches
- Fuel Filters
- Fuel Hoses
- Fuel Injection
- Fuel Pumps
- Gaskets & Seals
- Glow Plugs
- Hose Line
- Ignition Coil
- Ignition Leads
- Ignition Modules
- Oil Caps & Breather Pipes
- Oil Filters
- Oil Pump & Kits
- Oil Seals
- Pistons Liners & Rings
- Pollen Filters
- Pulleys
- Rotor Arms
- Spark Plugs
- Super Chargers
- Throttle Bodies
- Exterior Accessories
- Air Compressor
- Antenna
- Auto Repair Crawlers/Creepers
- Car Covers
- Emergency Road Side Kits
- License Plates
- Motorcycle Cleaning Kits
- Mounts
- Paint Sealants
- Rain Repellent
- Recovery Boards
- Repair Tools
- Roof Racks
- Shackles
- Side Skirts
- Spoilers
- Sunroof Deflectors
- Towing & Hitches
- Tyre Covers
- Tyre Deflator
- Tyre Inflator
- Winches & Straps
- Window Tint
- Wiper Blades
- Wiper Nozzle
- Engine/Interior Cooling
- Accumulators & Receiver Driers
- Actuators
- Air Conditioning Controls
- Air Conditioning Refrigerants
- Blowers
- Cabin Suction Fans
- Compressors
- Condenser
- Evaporators
- Expansion Tanks
- Expansion Valves
- Fan Clutches
- Fans
- Heater Cables
- Heater Controls
- Heater Matrix
- Heater Motors
- Intercoolers
- Oil Coolers & Car Oil Pipes
- Pipes & Hoses
- Pumps & Gaskets
- Radiator Caps
- Suspension Parts
- Air Suspension
- Anti Roll Bar & Components
- Boots & Gaskets
- Bushes
- Centre Drag Links
- Column Parts & Couplings
- Dampers
- Driveshafts
- Engine Mounts
- Idler & Pitman Arms
- Lowering Springs
- Pas Pumps
- Rear Axle
- Rear Axle Carriers
- Shock Absorbers
- Side Rods
- Springs
- Stabilizer Links
- Steering Boxes
- Steering Pumps
- Steering Racks & Mounts
- Power & Hand Tools
- Other Tools
- Knives
- Punches
- Clamps
- Drills
- Dust Collectors & Air Cleaners
- Engraving Tools
- Grinders
- Hot Air Guns and Glue Guns
- Polishers and Polishing Accessories
- Rotary Tools
- Electric Cutter
- Sanders, Sander Accessories and Sand Blasters
- Saws
- Soldering & Desoldering Equipment
- Tool Sets
- Abrasive Wheels & Discs
- Air Tool Accessories
- Blades
- Cordless Tool Accessories
- Drill Accessories
- Drill Bits and Sets
- Grinder & Accessories
- Hole Saws
- Pressure Washer
- Saw Accessories
- Electric Screwdriver
- Axes, Crimpers and Crowbars
- Chisels
- Cutters
- Files & Rasps
- Hammers & Mallets
- Hand Drills & Pumps
- Pliers & Pincers
- Wrenches
- Cleaning/Care Accessories
- Gloves
- Toilet Brush
- Apron
- Bin Liner
- Bottle Brush
- Broom
- Brush
- Brush/Dustpan Set
- Bucket
- Cart
- Cleaning Cloth
- Cleaning Pad
- Descaler
- Duster
- Dustpan
- Floor Pad
- Garbage Bin
- Lint Brush/Roller
- Mask
- Mop
- Mop/Bucket Set
- Other Cleaning/Care Accessories
- Recycle Bin
- Rubble Sack
- Safety Cone / Caution Floor Sign
- Scraper
- Scrub
- Sponge
- Spray Bottle
- Squeegee
- Sweeper
- Home Automation Devices
- Light Sockets
- Outlets & Accessories
- Plugs
- Power Strips
- Terminals
- Testers
- Electrical & Solar
- Recessed Lighting
- Switches
- Ballasts
- Breakers, Load Centers & Fuses
- Cables
- Cord Management
- Cords, Adapters & Multi-Outlets
- Door Chimes & Bells
- Electric Motors
- Electrical Boxes, Conduit & Fittings
- Electrical Connectors
- Electrical Wire
- Antiques & Collectables
- Cookbooks, Food & Drink
- Family History & Nostalgia
- Gardening
- Handicrafts, Decorative Arts & Crafts
- Hobbies, Quizzes & Games
- Home Improvement & Design
- Humour
- Lifestyle & Personal Style Guides
- Miscellaneous Items
- Natural History
- Sports & Outdoor Recreation
- Transport
- Travel & Holiday
- Pet Health/Hygiene
- Digestion
- Vitamins
- Eye Care
- Anti-Bacterial Treatments
- Anti-Fungus Treatments
- Anti-Stress
- Cooling Aids
- Dental Care
- Deodorants/Disinfectants/Deodorizers
- Ear Care
- Fish Fin Parasite Treatments
- Flea Combs
- Flea Shampoos
- Flea/Tick Treatments
- Food Mats
- General Health
- Grass Supplements
- Hair Pick Up
- Insect Repellents
- Joint Support
- Lint Roller
- Litter - Clay
- Litter - Disposal Bags
- Litter - Fibres
- Litter - Fresheners
- Litter - Gravel/Sand
- Litter - House
- Litter - Lids
- Litter - Papers
- Litter - Sand
- Litter - Shovels/Dustpans
- Litter - Silicate
- Litter - Tray Liners
- Litter - Trays
- Litter - Wood
- Malt Supplements
- Minerals
- Mite Treatments
- Other Health/Hygiene
- Pads
- Pet Diapers
- Sanitary Towels
- Scooper
- Skin Care
- Stain/Odor Removers
- Tools & Accessories
- Tooth Brush
- Tooth Paste
- Aqua Scaping & Decor - Stones & Rocks
- Aqua Scaping & Decor - Wood
- Aquarium - Accessories
- Aquarium - Air Pumps & Accessories
- Aquarium - Co2 Systems
- Aquarium - Dosing & Auto Top-Up
- Aquarium - Filters
- Aquarium - Heaters
- Aquarium - Hoods
- Aquarium - Lighting
- Aquarium - Nano Accessories
- Aquarium - Pumps & Wave Makers
- Aquarium - Skimmers & Reactors
- Aquarium - Spare Parts
- Aquarium - U/V & Ozone
- Aquarium - Water Testing
- Aquariums
- Aquatic/Fish Food
- Automatic Feeders
- Cleaning Tools
- Deodorizers
- Fish Bowls
- Hydrometers
- Medications
- Plant Care - Accessories
- Plant Care - Additives & Fertilizers
- Plant Care - Co2
- Plant Care - Soil & Substrates
- Plant Care - Tools
- Aquatic Accessories
- Thermometer
- Additives & Conditioners
- Aqua Scaping & Decor - Artificial Corals
- Aqua Scaping & Decor - Artificial Plants
- Aqua Scaping & Decor - Artificial Stones
- Aqua Scaping & Decor - Artificial Wood
- Aqua Scaping & Decor - Covers & Background
- Aqua Scaping & Decor - Decorative Marbles
- Aqua Scaping & Decor - Live Aquarium Plants
- Aqua Scaping & Decor - Ornaments
- Aqua Scaping & Decor - Sand - Gravel & Stones
- Pet Housing/Bedding
- Pet Housing/Bedding Accessories
- Baskets/Boxes/Cages
- Beds/Mattress/Mats
- Cages
- Carriers/Strollers
- Covers/Liners
- Cushions/Pillows
- Elevated/Outdoor Beds
- Floor Mesh
- Heat Lamps
- Heat Pads
- Houses/Doors
- Kennel Accessories
- Kennels/Crates/Pens/Condos
- Nesting Material
- Nests
- Open Trays
- Orthopaedic Beds
- Plaid/Blankets
- Seat Protection Covers
- Sofas & Chairs
- Spinner Wheel
- Stairs & Steps
- Stands
- Steps/Rams
- Reptile & Amphibian Accessories
- Deodorizers
- Terrariums
- Basking Spot Lamps
- Breeding Supplies
- Decor - Artificial
- Decor - Backgrounds
- Decor - Hides
- Decor - Natural Branches
- Decor - Substrates
- Dishes
- Fixtures & Equipment
- Food
- Handling Equipment
- Health & Hygiene
- Heat Globes
- Heating & Lighting
- Humidity Equipment
- Night & Moonlight Globes
- Pad/Cable/Rock
- Office Electronics
- Bar Code Scanners
- Basic Calculators
- Cash Registers
- Copiers
- Electronic Dictionaries, Thesauri & Translators
- Electronic White Boards
- Fax Machines
- Financial & Business Calculators
- Graphing Calculators
- Label Makers
- Laminators
- Laser Pointers
- Overhead Projectors
- Postal Scales
- Presentation Pointers
- Presentation Remotes
- Printing Calculators
- Scientific Calculators
- Shredders
- Typewriters
- Video Projectors
- Corded Phone
Video Games Accessories
Home Audio Equipment
Home Appliances Accessories
Small Appliances
Specialty Electrics
Large Appliances
Cutlery & Flatware
Bar
Storage & Organization
Coffee & Tea Appliances
Cycling
Strength Training Equipment
Boxing & MMA
Diving & Snorkelling
Sports & Outdoor Play
Hobbies
Baby Furnishing
Feeding & Training Accessories
Baby Safety Equipment
Fresh Vegetables
Fresh Fruits
Canned, Dry & Packaged Foods
Beverages
Body Parts
Engine Parts
Exterior Accessories
Engine/Interior Cooling
Suspension Parts
Power & Hand Tools
Cleaning/Care Accessories
Electrical & Solar
Lifestyle, Sport & Leisure
Pet Health/Hygiene
Aquatic Accessories
Pet Housing/Bedding
Reptile & Amphibian Accessories
Office Electronics

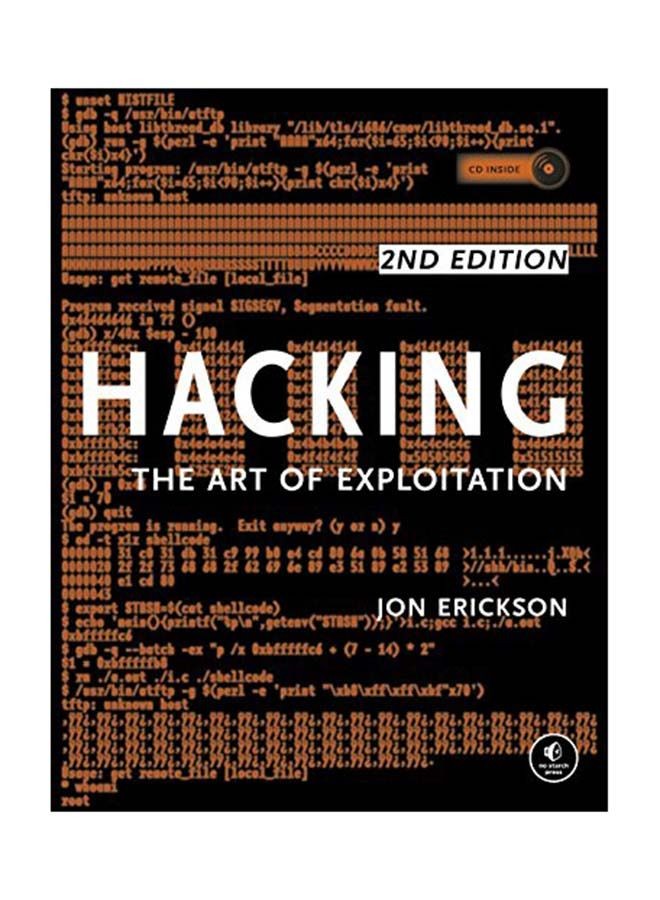
Hacking: The Art Of Exploitation, 2nd Edition Paperback
Key Features
- FREE RETURNS Get free returns on eligible items
- TRUSTED SHIPPING Free shipping when you spend $30 and above on express items
- CONTACTLESS DELIVERY Your delivery will be left at your door, valid on prepaid orders only.
- FREE VIP SHIPPING As a zimpot VIP, you get free next day delivery on express items
Technical Details
| Model number: | N21331324A |
|---|---|
| EAN: | N21331324A |
| Part Number: | N21331324A |
| Seller SKU: | ZW21331324A |
| Condition: | New |
| Origin: | United States |
| Availability: | In Stock |
| Minimum order quantity: | 1 |
| Shipping weight: | 500.00 g |
| Date first listed on zimpot : | Apr 30, 2021 |
Return & Refund Policy
Thanks for shopping at My Shop.
If you are not entirely satisfied with your purchase, we're here to help.
Returns
You have 30 (change this) calendar days to return an item from the date you received it.
To be eligible for a return, your item must be unused and in the same condition that you received it.
Your item must be in the original packaging.
Your item needs to have the receipt or proof of purchase.
No reviews
Related Items
Return & Refund Policy
Thanks for shopping at My Shop.
If you are not entirely satisfied with your purchase, we're here to help.
Returns
You have 30 (change this) calendar days to return an item from the date you received it.
To be eligible for a return, your item must be unused and in the same condition that you received it.
Your item must be in the original packaging.
Your item needs to have the receipt or proof of purchase.
Tengai Verified Purchase | 1 year ago
Tengai Verified Purchase | 1 year ago
fast and reliable
Tengai Verified Purchase | 1 year ago
thank you i like it
Customer Verified Purchase | 2 years ago
I have received the product in good packaging
Customer Verified Purchase | 4 years ago
ndafarira service yavo zvasvika nenguva
Customer Verified Purchase | 4 years ago
best service
Customer Verified Purchase | 4 years ago
I have ordered from zimpot countless time and I have never had a problem, delivery is fast and products a great. One time i got a defective smart watch they refunded me my amount with no hustle.
Customer Verified Purchase | 4 years ago
Well packed
Customer Verified Purchase | 4 years ago
Best seller
Customer Verified Purchase | 4 years ago
I was very hesitant about buying an apple iPhone from zimpot, but since I wanted to buy iPhone with facetime in Dubai, I had no option but to buy from zimpot. I was very reluctant and was not sure whether the product is genuine or is it per the descr